Will the SCO states’ efforts to address “territorial disputes” in cyberspace determine the future of international human rights law?
Key Takeaways
- The International Code of Conduct for Information Security (the “Code”) is an international effort to develop norms of behaviour in the digital space, submitted to the UN General Assembly in 2011 and in revised form in 2015 by member states of the Shanghai Cooperation Organization (SCO).
- With its connections to the SCO and existing content, the Code raises significant concerns under international human rights law.
- The SCO states may succeed in building consensus around the Code given the post-Snowden international political environment.
- The SCO states may view the Code as a vehicle to redefine application of international human rights law in order to extend SCO notions of sovereignty and territorial integrity to the digital space.
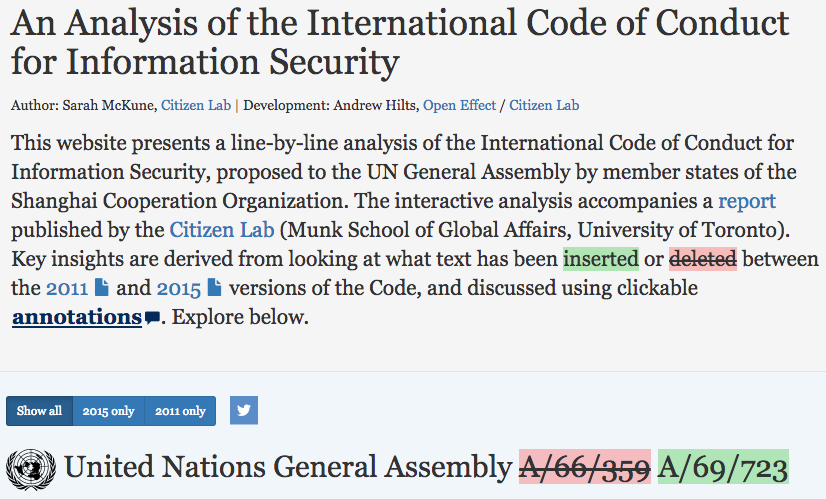
- An interactive feature accompanying this article illustrates the differences between the 2011 and 2015 versions of the Code. It also allows readers to select particular provisions of the Code to display analysis of the selected language.
Introduction
As the United Nations General Assembly begins its milestone 70th session, international digital security is high on the agenda. One starting point for discussion is likely to be the International Code of Conduct for Information Security (the “Code”), which was submitted for consideration to the UN General Assembly in January 2015 by the founding member states of the Shanghai Cooperation Organization (SCO) — China, Russia, Kazakhstan, Kyrgyzstan, Tajikistan, and Uzbekistan (the “SCO states”). According to its sponsors, the Code is intended “to push forward the international debate on international norms on information security, and help forge an early consensus on this issue.”1
A slightly different version of the Code was originally offered to the UN General Assembly by China, Russia, Tajikistan, and Uzbekistan in September 2011. It was revised for 2015 by purportedly “taking into full consideration the comments and suggestions from all parties.” This time around, however, the international debate has shifted significantly, with renewed efforts to develop international consensus on “information security” informed by both the December 2012 World Conference on International Telecommunications (WCIT) meeting and the June 2013 Snowden disclosures. Accusations that the US and its Five Eyes partners exploit their “dominant position in the information space” have gained credibility, while matters of equitable Internet governance and prevention of cyber attack and intrusion are of the utmost concern to all states. A code of conduct that attempts to address these issues is likely to generate significant interest.
Yet, four years after the first iteration of the Code, the document still raises serious concerns with respect to human rights. The narrative of the Code emphasizes state sovereignty and territoriality in the digital space above all else, and is dominated by intelligence, national security, and regime stability imperatives. Perhaps most worrisome, trends embodied by the SCO and reflected in the Code itself suggest a strategic revisionism on the part of the SCO states towards international human rights law.
As efforts to generate consensus around the Code proceed, it is essential to assess its potential long-term outcomes. While the Code effectively captures the sentiment and fears of the international community regarding misuse of the digital space, it ultimately represents a fundamental challenge to the flourishing of global thought and discourse through the Internet, as well as to the established framework of international human rights law.
The interactive feature accompanying this article here illustrates the differences between the 2011 and 2015 versions of the Code. It also allows readers to select particular provisions of the Code to display analysis of the selected language. The feature provides additional detail regarding the issues raised in this article.
Roots of the Code in the SCO
The Code is largely a product of regional norm-building undertaken within the SCO. Since its establishment in 2001, the SCO has served as a key forum for its member states to explore normative and legal consensus, as well as practical cooperation, regarding non-traditional security threats.2 Initially the SCO focused on those threats embodied by the concept of the “Three Evils”3 — terrorism, separatism, and extremism4 — but the organization soon added information security to its agenda as well. The SCO offers a platform for a “soft launch” of the principles and practices that the SCO governments consider essential to regime stability in the face of these threats. Once these principles and practices have acquired traction regionally, they provide a foundation for building consensus at the international level.
A “SCO plan of action to ensure international information security” was first agreed upon by heads of state in August 2007.5 Following initiatives laid out in that plan, the SCO states agreed upon a formal convention for information security in June 2009.6 This convention identified main threats in and defined key concepts related to the information space. In June 2011, the states noted their intent to press for a similar agreement — an “international code of conduct” — to address information security in the international arena,7 and the Code was born.
Russia’s involvement in this process is particularly noteworthy. As far back as 1999, after its initial introduction in 1998 of the now-yearly UN General Assembly resolution on “Developments in the field of information and telecommunications in the context of international security,”8 Russia submitted to the UN Secretary-General a set of proposed “principles of international information security.”9 In an additional submission Russia identified the “main threats” to that security.10 This early emphasis on information security appears to relate to the work of Vladislav Sherstyuk, a former KGB officer and a general within FAPSI11 (Russia’s electronic intelligence agency) during the 1990s.12 The generals of FAPSI essentially defined the country’s approach to information security. Sherstyuk was appointed director of FAPSI in 1998, and in 1999 he became chief of the committee on information security of the Russian Security Council.13 Sherstyuk was responsible for developing Russian policy in this area, including the drafting of the Doctrine of Information Security14 that was ultimately approved by the Russian President in 2000.15
While these information security principles did not advance at the international level at such an early stage, within the regional framework of the SCO they flourished and solidified, strengthened by the interest and participation of China. The concepts and threats identified by Russia — including “use of information to undermine the political, economic and social system of other States,” “domination or control in the information area,” and “unauthorized transboundary influence through information”16 — are clearly integrated within the SCO Agreement on Cooperation in the Field of International Information Security. They have now reappeared, refined, in the form of the Code.
This history is significant in light of the serious human rights challenges associated with the SCO and its member states. The SCO framework is built upon normative agreements that present a regional alternative to established principles of international human rights law, as well as practices to confront non-traditional security threats that infringe upon human rights.17 They recognize that information security includes control of content and exchange through digital media. The Code affirms and extends those principles and practices. (See interactive analysis.)
What’s new for 2015?
A number of developments affecting the digital space have taken place since 2011 which have influenced the Code and international diplomacy. Most prominent among these are the Snowden disclosures and their ongoing fallout. Other important developments include heated debates over the future of Internet governance, public reporting of major digital security breaches within the private sector and government, and bilateral (e.g., US-China) and multilateral (e.g., UN Group of Governmental Experts) grappling with the issue of digital attacks and appropriate state responses. Leadership changes in Russia and China have also influenced the digital environment, with Vladimir Putin returning to power in 2012 and Xi Jinping assuming the presidency in 2013. Both leaders have overseen major domestic crackdowns with heavy emphasis on information controls.
The Code reflects these changes in its bolder stance on, and more urgent call for, international consensus on digital norms. Major themes represented in the revised Code are:
Appreciation for the UN Group of Governmental Experts on Developments in the Field of Information and Telecommunications in the Context of International Security (GGE)
While the GGE existed prior to the issuance of the Code in 2011, it was not mentioned in the original document. The 2015 version of the Code, in contrast, makes substantial reference to the GGE’s work, indicating a favorable view by the SCO states of the work undertaken over the past four years in that forum. This appreciation for the GGE is likely the result of its treatment of issues of critical importance to the SCO states, namely, recognition of sovereignty and territoriality in the digital space, and recommendation of voluntary, non-binding norms of state behaviour and confidence-building measures to prevent conflict between states. As a body comprised of expert state representatives and reflecting “equitable geographic distribution,” it offers substantial authority for norm development on these issues. The Code recognizes this fact in its reference to paragraph 16 of the GGE report, which concerns continuation of the norm-building process. (See interactive analysis.)
Digging in on Internet governance and “dominance” in the digital space
The 2015 version of the Code makes stronger reference to Internet governance and equal rights of states in matters of digital policy, drawing on World Summit on the Information Society (WSIS) outcomes for support. It also resurfaces the contentious issues raised during the 2012 WCIT meeting in Dubai.18 (See interactive analysis.) Both versions of the Code endorsed the view that “policy authority for Internet-related public issues is the sovereign right of States,” but the 2015 version goes further, noting that that “states must play the same role in, and carry equal responsibility for, international governance of the Internet, its security, continuity and stability of operation, and its development.”
The principle of Internet policy authority as the sovereign right of states has been hotly debated, particularly at WCIT 2012. The U.S. and other states have argued that Internet policy should not be exclusively state-determined (e.g., in fora such as the International Telecommunication Union); rather, it should rely upon a multistakeholder model of Internet governance.19 Russia, China, and many developing countries have taken the view that such a position naturally favors the West, which already holds significant influence over the Internet given the role of ICANN and major US-based ICT companies. Andrey V. Krutskikh, the Russian government’s representative at WCIT 2012, stated after the event:
Dealing with ICTs without including the Internet is absurd. It is mandatory to consider these two phenomena together . . . . [T]he system should be made operational, instead of trying to freeze the current situation and claim that the system is working – we should acknowledge that it is not working well. And the discussion that took place in Dubai was focused exactly on this – that the system is not working well. . . . [W]e should coin a new system together. . . . And everybody – Chinese, Americans, NATO-allies — should engage in the process [as opposed to just] attempting to preserve their present advantages.20
The issue of participation in Internet governance is closely linked to that of “dominance” in the digital space, an SCO concept of Russian origin that is also highlighted in the Code. The Code flags inequalities and dominant-state advantages in the information space, including with respect to control of ICT supply chains, as serious threats to national security. This position has achieved wider resonance in the international community following the Snowden disclosures, and could generate greater interest in the Code despite its significant rights implications.
International human rights law revisionism
The evolution of the Code’s sole substantive provision regarding human rights — paragraph 2(f) in the 2011 version and 2(7) in the 2015 version — is instructive concerning the strategic outlook of the SCO states on international human rights law. The 2011 version discussed digital rights by suggesting they could be curtailed to “comply[] with relevant national laws and regulations” — an easy target for criticism given the pervasive rights abuses tolerated, if not authorized or required, by the SCO states’ legal and regulatory regimes. The 2015 version replaces the reference to national standards with reference to international law, namely, the International Covenant on Civil and Political Rights (ICCPR), thereby removing specific language that might have dissuaded states concerned with digital rights from accepting the Code.
In elaborating on the application of international human rights law, however, the Code focuses primarily on restrictions on freedom of expression available to states under the law, quoting ICCPR article 19(3). This selective invocation of the law suggests the SCO states’ intention to frame existing domestic information controls as compatible with international human rights law. Such an interpretation, however, is not consistent with objective application of the law. The UN Human Rights Committee has noted that general reservations to the rights guaranteed in ICCPR article 19(2) are incompatible with the object and purpose of the treaty,21 and that restrictions imposed on the basis of article 19(3) “may not put in jeopardy the right itself. . . . [T]he relation between right and restriction and between norm and exception must not be reversed.”22 Moreover, restrictions pursuant to article 19(3) “must conform to the strict tests of necessity and proportionality.”23 Pervasive information controls in the SCO states, which restrict dissemination of content deemed politically sensitive by the government and in some instances result in criminal punishment of legitimate expression, do not credibly meet these standards.
Additionally, the lack of reference to the right to privacy is noteworthy. Privacy has been high on the agenda of the UN since the Snowden disclosures, and was highlighted in the very same General Assembly resolution drawn on in the Code for the proposition that “the rights of an individual in the offline environment must also be protected in the online environment.”24 Indeed, the UN Human Rights Council has now established a special procedure specifically devoted to the right to privacy.25 The failure to mention this right suggests an unwillingness by the SCO states to concretely address state surveillance.
To what end?
The purpose of the SCO states in advancing the Code is ultimately the key issue for consideration. Indeed, the progress made in the GGE on issues of practical and even military significance — recognized in the Code itself — raises the question: what additional benefits do the SCO states hope to obtain by resuscitating the Code at the wider UN level?
On one hand, as others have written, the Code has allowed the SCO states to obtain a sort of “diplomatic high ground” regarding digital norms, staking a claim on normative principles emerging at the international level by drawing upon those already well-developed within the SCO.26 China, for example, has frequently referenced the Code when responding to allegations regarding its activity in the digital space, including involvement in digital espionage or attack.27 China has invoked the Code as though it were prima facie evidence of the good faith and positive contributions of the Chinese government when it comes to cyberspace — a standard to which other states should aspire.
However, the Code appears intended to achieve more than a declaratory effect. It is one element of the SCO states’ bifurcated approach to international diplomacy on information security. The SCO states have utilized the GGE and bilateral negotiations to achieve concrete results regarding state-to-state interaction and confrontation or hostilities in the digital space. At the same time, they have actively engaged the UN General Assembly, its First Committee, and other multilateral fora to generate international acceptance of norms conducive to domestic policy on digital rights. These norms concern the sensitive systemic issues of what constitutes appropriate policy for citizens’ digital participation, who holds that policy authority, and how to resolve such policy with international law and current realities of ICT usage.
Russia and China in particular are vocal proponents of “digital” or “Internet” sovereignty, treating the digital space as territory disputed between states and properly subject to domestic control.28 Russian lawmakers have described the Internet as “break[ing] down borders and undermin[ing] the idea of sovereignty,” with the ability to “encroach on internal sovereign interests and destroy national security.”29 China, meanwhile, has stated:
The sovereignty principle in cyber space includes at least the following factors: states own jurisdiction over the ICT infrastructure and activities within their territories; national governments are entitled to making public policies for the Internet based on their national conditions; no country shall use the Internet to interfere in other countries’ internal affairs or undermine other countries’ interests.30
This position is in line with China’s assertion of unique requirements presented by its “history, culture and social system” (as flagged in the Code), and its pushback against purportedly Western-dominated “universal values,” which President Xi has identified as contrary to Communist Party ideology.31
Importantly, the Code offers a chance to redefine application of international human rights law in order to extend SCO notions of sovereignty and territorial integrity to the digital space. SCO state practice and normative agreements underscore these states’ baseline principle that a state may circumscribe, surveil, or otherwise control any content or digital medium utilized within its territory at its discretion. Such control is deemed essential for maintenance of domestic stability and regime preservation in light of the proximity and influence afforded to individuals, states, and other actors by the Internet.32 Yet, it is also in direct contradiction with established principles of international human rights law, contravening rights including privacy and freedoms of opinion and expression, as well as undermining the agency of domestic populations.
The Code may be viewed as an attempt to square these diametrically opposed principles, to build consensus within the international community around a revised interpretation and application of international human rights law to favor the SCO states’ domestic agendas. It is noteworthy that the Chinese government, which presented both versions of the Code to the UN, has already attempted in other contexts to bolster its legitimacy on contested issues by relying on the purported existence of “consensus,” as embodied in codes of conduct or similar agreements.33 For example, the government has engaged in massive crackdowns on rights defense lawyers in recent years.34 Alongside these crackdowns, China’s largest bar association, the government-controlled All China Lawyers Association, has revised its “code of conduct” for lawyers, reflecting new nationwide standards of practice that would effectively censure the sensitive work of rights defense lawyers.35
While the SCO states have accepted the premise that “rights of an individual in the offline environment must also be protected in the online environment,” if those rights are only those recognized in existing domestic policy and practice, rather than international law, serious challenges remain. Attempts to frame the Code as “consensus,” relying on either the support or the silence of the international community, may erode protections for human rights guaranteed under international law. If the international community disagrees with this proposition, it will need to critically engage the Code and explicitly question its international human rights law ramifications.
Acknowledgements
Special thanks to Irina Borogan of Agentura.ru for her expert input and sharing of interview material regarding the evolution of information security in Russia. Thank you to Igor Valentovitch for translation assistance, and to Ron Deibert and John Scott-Railton for substantive feedback.
1 U.N. General Assembly, “Letter dated 9 January 2015 from the Permanent Representatives of China, Kazakhstan, Kyrgyzstan, the Russian Federation, Tajikistan and Uzbekistan to the United Nations addressed to the Secretary-General,” U.N. Doc. A/69/273 (2015), http://www.un.org/Docs/journal/asp/ws.asp?m=A/69/723.
2 See generally Human Rights in China, Counter-Terrorism and Human Rights: The Impact of the Shanghai Cooperation Organization (New York: Human Rights in China, 2011), http://www.hrichina.org/en/publications/hric-report/counter-terrorism-and-human-rights-impact-shanghai-cooperation-organization.
4 See Shanghai Cooperation Organization (SCO), The Shanghai Convention on Combating Terrorism, Separatism and Extremism, June 15, 2001, http://www.sectsco.org/EN123/show.asp?id=68.
5 U.N. General Assembly, “Developments in the field of information and telecommunications in the context of international security: Report of the Secretary-General,” U.N. Doc. A/64/129 (2009), reply received from Kazakhstan, para. 9, http://www.un.org/Docs/journal/asp/ws.asp?m=A/64/129.
6 SCO, Agreement on Cooperation in the Field of International Information Security, June 16, 2009, available at https://ccdcoe.org/sites/default/files/documents/SCO-090616-IISAgreement.pdf.
7 “Speech by Dmitry Medvedev at a meeting of the Shanghai Cooperation Organisation Council of Heads of State in expanded format,” June 15, 2011, http://en.kremlin.ru/events/president/transcripts/11578 (“The Shanghai Cooperation Organisation member countries, based on the agreement on cooperation on international information security, make a contribution to the international community’s efforts in this area. One of the items on the agenda today is to approve the proposal to submit to the 66th session of the UN General Assembly a draft resolution on an international code of conduct in the area of information security. This is clearly an important initiative and it shows our common desire to find a solution to this complex problem.”).
8 U.N. General Assembly, Resolution 53/70, “Developments in the field of information and telecommunications in the context of international security,” U.N. Doc. A/RES/53/70 (1998), http://www.un.org/Docs/journal/asp/ws.asp?m=A/res/53/70.
9 U.N. General Assembly, “Developments in the field of information and telecommunications in the context of international security: Report of the Secretary-General,” U.N. Doc. A/55/140 (2000), reply received from the Russian Federation (dated May 12, 1999), http://www.un.org/Docs/journal/asp/ws.asp?m=A/55/140.
10 U.N. General Assembly, “Developments in the field of information and telecommunications in the context of international security: Report of the Secretary-General,” U.N. Doc. A/54/213 (1999), reply received from the Russian Federation (dated June 9, 1999), http://www.un.org/Docs/journal/asp/ws.asp?m=A/54/213.
11 FAPSI is the acronym for Russia’s Federal Agency for Government Communications & Information; the agency was disbanded in 2003. It was the Russian analogue to the United States National Security Agency. See generally “Federal Agency for Government Communications & Information (FAPSI),” Federation of American Scientists, http://fas.org/irp/world/russia/fapsi/.
12 Andrei Soldatov and Irina Borogan, The Red Web: The Struggle Between Russia’s Digital Dictators and the New Online Revolutionaries (New York: PublicAffairs, 2015), 224-26.
14 Information Security Doctrine of the Russian Federation, approved by President of the Russian Federation Vladimir Putin on September 9, 2000, http://archive.mid.ru//bdomp/ns-osndoc.nsf/1e5f0de28fe77fdcc32575d900298676/2deaa9ee15ddd24bc32575d9002c442b!OpenDocument.
15 Soldatov and Borogan, supra n. 12.
16 U.N. General Assembly, “Developments in the field of information and telecommunications in the context of international security: Report of the Secretary-General,” U.N. Doc. A/55/140 (2000), reply received from the Russian Federation (dated May 12, 1999), http://www.un.org/Docs/journal/asp/ws.asp?m=A/55/140.
17 See generally Human Rights in China, supra n. 2.
18 See, e.g., Milton Mueller, “ITU Phobia: Why WCIT was Derailed,” Internet Governance Project, December 18, 2012, http://www.internetgovernance.org/2012/12/18/itu-phobia-why-wcit-was-derailed/; David P. Fidler, “Internet Governance and International Law: The Controversy Concerning Revision of the International Telecommunication Regulations,” ASIL Insights, vol. 17 no. 6, February 7, 2013, http://www.asil.org/insights/volume/17/issue/6/internet-governance-and-international-law-controversy-concerning-revision.
19 U.S. Department of State, “U.S. Intervention at the World Conference on International Telecommunications,” December 13, 2012, http://www.state.gov/r/pa/prs/ps/2012/12/202037.htm.
20 Andrey V. Krutskikh, special coordinator on issues related to the political usage of ICTs in the Russian Ministry of Foreign Affairs, interview by Irina Borogan, Agentura.ru, February 6, 2013, on file with author. Krutskikh later became the Special Representative of the President of the Russian Federation for International Cooperation in Information Security. He has served as the state’s representative at every meeting of the GGE.
21 U.N. Human Rights Committee, General comment No. 34, “Article 19: Freedoms of opinion and expression,” U.N. Doc. CCPR/C/GC/34 (2011), para. 6, http://www2.ohchr.org/english/bodies/hrc/docs/gc34.pdf.
24 U.N. General Assembly, Resolution 68/167, “The right to privacy in the digital age,” U.N. Doc. A/RES/68/167 (2013), http://www.un.org/Docs/journal/asp/ws.asp?m=A/RES/68/167. In this resolution the General Assembly affirmed that “the same rights that people have offline must also be protected online, including the right to privacy” (para. 3), and called upon states “[t]o respect and protect the right to privacy, including in the context of digital communication” (para. 4[a]).
25 See U.N. Human Rights Council, Resolution 28/16, “The right to privacy in the digital age,” U.N. Doc. A/HRC/RES/28/16 (2015), para. 4, http://www.un.org/Docs/journal/asp/ws.asp?m=A/HRC/RES/28/16.
26 See Paul Meyer, “Seizing the Diplomatic Initiative to Control Cyber Conflict,” The Washington Quarterly, August 3, 2015, http://twq.elliott.gwu.edu/seizing-diplomatic-initiative-control-cyber-conflict; see also Kristen Eichensehr, “International Cyber Governance: Engagement Without Agreement?,” Just Security, February 2, 2015, https://www.justsecurity.org/19599/international-cyber-governance-engagement-agreement/.
27 See, e.g., Ministry of Foreign Affairs of the People’s Republic of China, “Foreign Ministry Spokesperson Hua Chunying’s Regular Press Conference,” March 3, 2015, http://www.fmprc.gov.cn/mfa_eng/xwfw_665399/s2510_665401/t1242257.shtml; Ministry of Foreign Affairs of the People’s Republic of China, “Foreign Ministry Spokesperson Hong Lei’s Regular Press Conference,” February 27, 2015, http://www.fmprc.gov.cn/mfa_eng/xwfw_665399/s2510_665401/t1241296.shtml; Ministry of Foreign Affairs of the People’s Republic of China, “Foreign Ministry Spokesperson Hua Chunying’s Regular Press Conference,” June 10, 2014, http://www.fmprc.gov.cn/mfa_eng/xwfw_665399/s2510_665401/t1164254.shtml.
28 See, e.g., Andrei Soldatov and Irina Borogan, “How Edward Snowden Inadvertently Helped Vladimir Putin’s Internet Crackdown,” BuzzFeed News, September 2, 2015, http://www.buzzfeed.com/andreisoldatov/how-edward-snowden-inadvertenly-helped-vladimir-putins-inter#.igygrz96G; Organizing Committee of the World Internet Conference, Wuzhen Declaration, November 21, 2014, available at http://www.scribd.com/doc/247566581/World-Internet-Conference-Draft-Declaration; Franz-Stefan Gady, “The Wuzhen Summit and Chinese Internet Sovereignty,” Huffington Post, December 9, 2014, http://www.huffingtonpost.com/franzstefan-gady/the-wuzhen-summit-and-chi_b_6287040.html.
29 Shaun Walker, “Russian data law fuels web surveillance fears,” The Guardian, September 1, 2015, http://www.theguardian.com/world/2015/sep/01/russia-internet-privacy-laws-control-web.
30 Ministry of Foreign Affairs of the People’s Republic of China, “Address by Vice Foreign Minister Li Baodong at the Opening Ceremony of the International Workshop on Information and Cyber Security,” June 5, 2014, http://www.fmprc.gov.cn/mfa_eng/wjbxw/t1162458.shtml.
31 Central Committee of the Communist Party of China’s General Office, “Communiqué on the Current State of the Ideological Sphere,” April 22, 2013, English translation by ChinaFile available at https://www.chinafile.com/document-9-chinafile-translation; see also Chris Buckley, “China’s New Leadership Takes Hard Line in Secret Memo,” New York Times, August 20, 2013, http://cn.nytimes.com/china/20130820/c20document/dual/; Shannon Tiezzi, “Ahead of Xi’s US Trip, China Defends Record on Human Rights,” The Diplomat, September 18, 2015, http://thediplomat.com/2015/09/ahead-of-xis-us-trip-china-defends-record-on-human-rights/; Human Rights in China, “Engaging China on Human Rights: The UN Labyrinth — HRIC Interview with Felice Gaer,” October 29, 2010, http://www.hrichina.org/en/content/3261.
32 It is telling that the original Russian principles presented to the UN Secretary General highlighted the need to “[d]evelop a procedure for the exchange of information on and the prevention of unauthorized transboundary influence through information.” U.N. General Assembly, “Developments in the field of information and telecommunications in the context of international security: Report of the Secretary-General,” U.N. Doc. A/55/140 (2000), reply received from the Russian Federation (dated May 12, 1999), Principle III(j), http://www.un.org/Docs/journal/asp/ws.asp?m=A/55/140. In 2013 Andrey V. Krutskikh, special coordinator on issues related to the political usage of ICTs in the Russian Ministry of Foreign Affairs — comparing US dominance over the Internet to its historical monopoly on the atomic bomb — flagged the importance to governments of “restor[ing] the balance in the system and ensur[ing] their own survival.” He also spoke of the need to prevent domestic acceptance of “harmful” influence “impose[d] through the Internet.” Andrey V. Krutskikh, supra n. 20.
33 In an interesting corollary, China has leveraged the existence of a “declaration of conduct” and related bilateral consultations in an attempt to preclude jurisdiction of an international arbitral tribunal in a case regarding the South China Sea. In the case of The Republic of the Philippines v. The People’s Republic of China (see http://www.pca-cpa.org/showpage65f2.html?pag_id=1529), China asserted (through a position paper) that the Permanent Court of Arbitration in the Hague has no jurisdiction, relying in part on a “mutual understanding” of the process for dispute resolution alleged to have been established between China and the Philippines on the basis of bilateral statements and the “Declaration on the Conduct of Parties in the South China Sea.” See Ministry of Foreign Affairs of the People’s Republic of China, “Position Paper of the Government of the People’s Republic of China on the Matter of Jurisdiction in the South China Sea Arbitration Initiated by the Republic of the Philippines,” December 7, 2014, http://www.fmprc.gov.cn/mfa_eng/zxxx_662805/t1217147.shtml. According to China, “The relevant provisions in the aforementioned bilateral instruments and the DOC are mutually reinforcing and form an agreement between China and the Philippines. On that basis, they have undertaken a mutual obligation to settle their relevant disputes through negotiations.” Ibid. at para. 39. The government has accused the Philippines of “violat[ing] consensus.” See “China opposes Philippines arbitration case,” CCTV.com, July 7, 2015, http://english.cntv.cn/2015/07/07/VIDE1436267888563988.shtml. One commentator has reflected: “While Manila sees its case as a test for international law, China dismisses it as a blatant grab for territory.” See Shannon Tiezzi, “In the Philippines’ South China Sea Case, Is International Law on Trial?,” The Diplomat, July 14, 2015, http://thediplomat.com/2015/07/in-the-philippines-south-china-sea-case-is-international-law-on-trial/. A similar calculus appears to apply to China’s handling of disputes in the digital space.
34 See Committee to Support Chinese Lawyers, Plight and Prospects: The Landscape for Cause Lawyers in China, September 2015, http://leitnercenter.org/files/Plight%20and%20Prospects_FULL%20FOR%20WEB.pdf; Committee to Support Chinese Lawyers, Legal Advocacy and the 2011 Crackdown in China, November 2011, http://www.csclawyers.org/letters/Legal%20Advocacy%20and%20the%202011%20Crackdown%20in%20China.pdf.
35 Such provisions include duties of “loyalty to the Party” and to “speak and act cautiously,” including requirements to “not call for, or unite others, to create a surge of public opinion and pressure on a case one is handling, or organize or participate in online gatherings, observations support or other inappropriate ways of using the Internet or other media, influencing judicial organs handling of a case.” See China Law Translate, “ACLA Explanation of Reforms to the Lawyers Code Of Conduct,” June 22, 2014, http://chinalawtranslate.com/acla-explanation-of-reforms-to-the-lawyers-code-of-conduct/?lang=en.